Check out our guest article by Jeevan Saini and a Toreon blog post covering 7 key learning principles to create our future threat modeling training
9 benefits of Threat Modeling is the second post in a series to educate those who are interested in a first experience with Threat Modeling
This post – What is Threat Modeling? – is the first in a series to educate those who are interested in a first experience with…
Check out our guest article by Koen Yskout and a Toreon blog post covering 7 key learning principles to create our future threat modeling training
Discover a guest article by Kim Wuyts covering “Keys to successful privacy threat modeling” and an update on our Threat Modeling Playbook.
In this months newsletter: A guest article by Brook Schoenfield, Webinar on 10 September: Up your game with the Threat Modeling Playbook ,A tip on “DREAD…
In this months newsletter: A guest article by Mikko Saario, Tip of the month, Curated resources covering threat modeling machine learning, A white paper on…
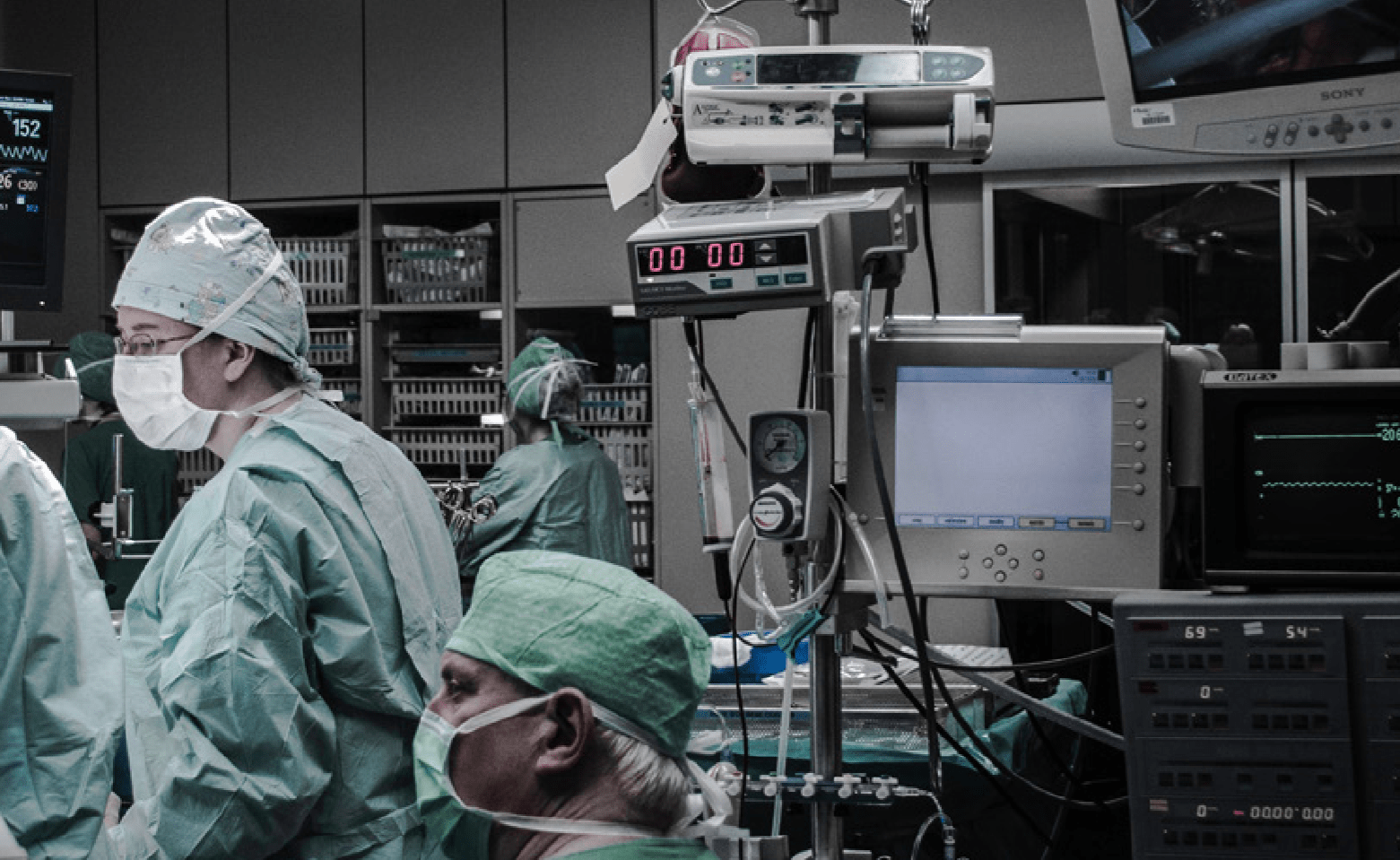
We’ve created a whitepaper, in collaboration with experts from the medical device community, to highlight how Threat Modeling can be applied in your field.
Threat modeling is as a discipline that fits really well in ICS and OT environments, to design and secure connected systems in a way that…